Open Banking is a new financial ecosystem that allows users to securely share their personal financial data with third-party providers, such as fintech companies or other financial institutions. By sharing this data, these organizations can provide personalized financial services to users. So, how is Open Banking data processed, and for what purposes is it used?
Open Banking: Consent Management
To provide and develop high-quality products and services, Third-Party Providers (TPPs) require user consent to access their financial data. From there, they filter and process this data for research purposes and to build new financial products and services.
Consent management is a sensitive matter that requires caution and expertise in both legal and technical aspects. Contrary to popular belief, consent management is not just a simple click or checking an “I Agree” box; it is a structured process implemented in compliance with regional and national regulations and directives, such as PSD2/PSD3 or GDPR in the EU.
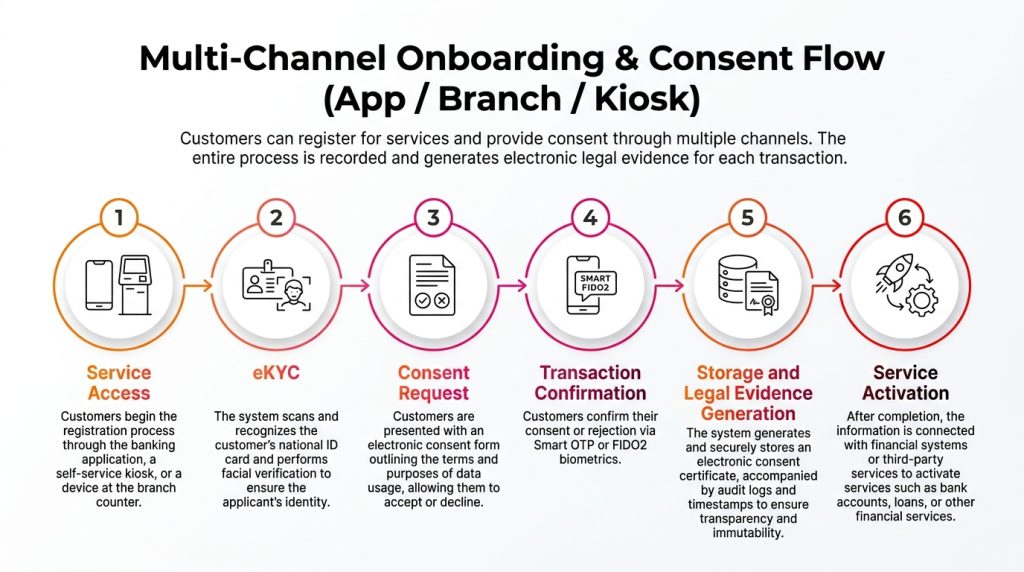
The consent management process in banking typically unfolds as follows:
- TPPs provide a notice regarding the purpose and the specific data to be collected, requesting consent from the customer.
- The customer agrees by confirming the request.
- Subsequently, data is transferred from an Account Information Service Provider (AISP) to the TPP, or from a Payment Initiation Service Provider (PISP) to the bank.
While different organizations may present data access agreements differently, this is the most common mechanism, often used in:
- Mobile authentication
- Banking account login
- Digital signatures
Understanding how data and information flow during the consent request process is a decisive factor for transparency and the success of organizations in Open Banking.
The Process of Managing Consent for Open Banking Data Sharing
The consent management process is generally divided into three stages:
a. Consent Stage
- Users receive a notification about the purpose and the data being used; they choose to either accept or decline.
- If they accept, users are notified of the duration of the data access authorization to ensure they remain in control of their information.
b. Authentication Stage
- The bank receives the information and requires the user to perform authentication to ensure data security.
- The user’s identity is verified. At this step, the TPP does not see the user’s authentication credentials.
c. Authorization Stage
- The bank notifies the user of the specific data that will be shared with the TPPs and allows the user to decline this notification.
- The user’s response is sent back to the bank.
Throughout every process, users always know who they are granting access to, for how long, and for what purpose. Most importantly, users can revoke consent at any time. The information available to users typically includes:
- Who is accessing their data: Name of the Third-Party Provider.
- For how long: The duration/timeframe.
- For what purpose: Account/payment details.
- Expiration process: When it will expire and how the user can revoke consent.
Open Banking Data Sharing: How Does It Work?
Open Banking allows third-party financial service providers to access information with user permission. Technically, this process is facilitated via Open APIs. Legally, the data-sharing process is overseen and governed by existing government regulations, such as the Payment Services Directive (PSD2) in the EU or the Open Banking Act in the UK.
However, as these regulations vary by region, the types of data shared through open banking services also differ. Typically, to ensure transparency and integrity, there are multiple layers of security and verification during the data exchange between financial institutions and TPPs. Data transmission is executed in a “heartbeat” thanks to APIs, ensuring a seamless, secure, and efficient experience.
Who Can Access Open Banking Data?
Not everyone can access data in Open Banking. To view this data, user consent is mandatory, and the TPP must be licensed. TPPs must also meet specific requirements before being authorized to access a user’s financial information.
Dedicated competent authorities are responsible for licensing TPPs to access user data. For example, in Australia, the Australian Competition and Consumer Commission (ACCC) is responsible for Open Banking data licensing.
These agencies ensure that personal financial data sharing does not violate the law while having the power to grant, modify, or revoke data collection licenses.
What Data is Collected in Open Banking?
The data collected by open banking service providers may vary depending on the regulations of each country/region and the type of service provided.
Regulators often set strict rules on the type of information that can be collected, limiting the scope to ensure TPPs only access what is strictly necessary. The most commonly collected data includes:
- Account holder information (Full name, date of birth, etc.)
- Personal or corporate codes
- Residential or contact addresses
- Business category or activity codes
- Financial liability information (active status)
- Account information related to deposits and securities
- Sometimes, other information such as employment status, workplace, etc.
How Does Open Banking Protect User Data?
Protecting data in Open Banking is a top priority for regulators and financial institutions. Security measures applied include:
- Strict Regulations/Legislation: Each country or region has its own rules and directives to ensure stable operations and data security (e.g., PSD2 in the EU, Open Banking Act in the UK).
- Advanced Security Technology: Banks and service providers use cutting-edge technologies such as encryption, Multi-Factor Authentication (MFA), and fraud detection to protect customer data.
- Risk Management: Financial organizations regularly assess and manage potential security risks while maintaining emergency response plans.
- Transparency: Users are always clearly informed about the type of data shared, the purpose of use, and how the data is protected.
- User Control: Users have the right to control their data sharing, including the right to revoke consent at any time.
However, alongside these protections, certain risks remain of concern to developers and users:
- Malware Threats: Malicious software can exploit security vulnerabilities to steal data.
- Data Breaches/Attacks
- Hackers: Cybercriminals constantly search for loopholes to infiltrate systems.
In summary, while risks cannot be entirely eliminated, current security measures are established to ensure user data is protected within the open banking system. Nevertheless, users should also protect themselves by using strong passwords, updating software regularly, and staying vigilant against phishing attacks.
Furthermore, empowering users to manage their open banking data is an excellent way for them to take responsibility for when and how they wish to provide their information. TPPs must clearly communicate the purpose and the data to be collected to ensure transparency and Open Banking data privacy.
Savyint and Savyint Consent Management
As an global technology company with extensive expertise in PKI, Cryptography, Blockchain, Electronic Identification, Authentication, Savyint proudly introduces Savyint Consent Management, specifically designed for the collection, storage, and transparency of user data rights.
As an international technology group with extensive expertise in PKI, Cryptography, Blockchain, Electronic Identification, Authentication, and Open Banking/Finance, Functioning as a central “Trust Engine,” this solution automates 100% of the processes for collecting, storing, and verifying data rights across the entire customer journey.
Savyint Consent Management enables enterprises to process sensitive data with total transparency, ensuring full compliance with global and local regulations such as Vietnam’s Personal Data Protection Law (No. 91/2025/QH15), Circular 64/2024/TT-NHNN, GDPR, FAPI 2.0…
Advanced Technologies of Savyint Consent Management:
- AI & Machine Learning: Automatically analyze user behavior and detect privacy violations or abnormal access activities.
- Zero Trust Architecture: A security model that requires continuous authentication and verification.
- Homomorphic Encryption: Enables data processing while the data remains encrypted, ensuring absolute data protection.
- Immutable Logs: Utilizes hash-chain technology to create tamper-proof audit logs that cannot be modified or deleted.
- PQC Ready: Encryption capabilities designed to protect data against future threats posed by quantum computing.
Connect with Savyint’s experts today to lead the way in the data security era and build sustainable digital trust!