As cyberattacks become increasingly sophisticated, traditional security models such as firewalls, VPNs, or trusted internal networks are no longer sufficient to protect modern enterprises. Zero Trust Architecture has emerged as a critical approach in today’s cybersecurity landscape, helping organizations strengthen protection across users, devices, applications, data, and digital transactions.
What is Zero Trust Architecture?
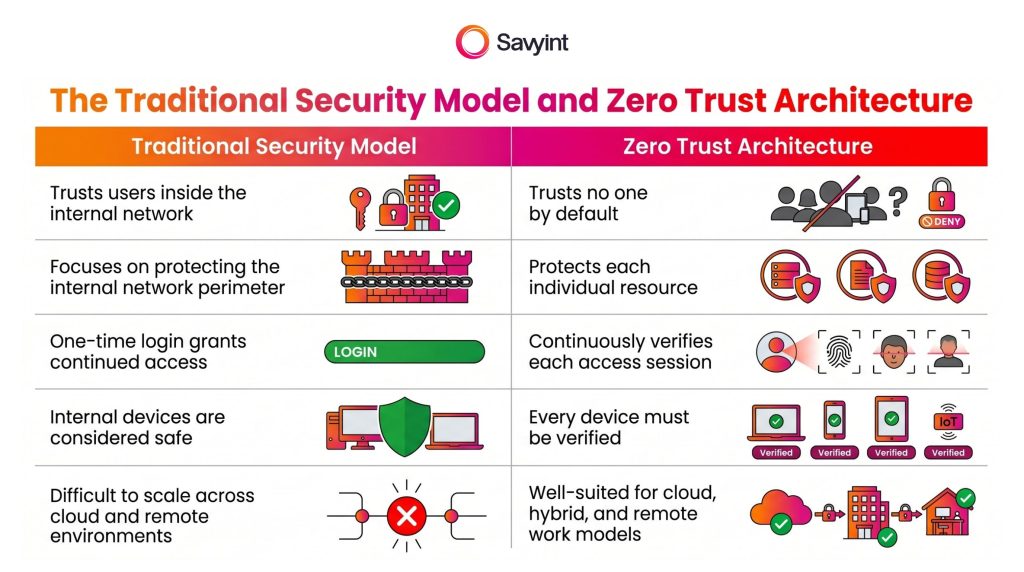
Zero Trust Architecture is a modern security model built on the principle of “never trust, always verify.” It is designed for today’s complex, distributed, and increasingly cloud-based IT environments.
Unlike traditional security models, Zero Trust requires every access request to be continuously verified, whether it originates from inside or outside the organization.
Zero Trust Architecture typically combines multiple security technologies, including:
- Identity and Access Management
- Multi-Factor Authentication
- Data encryption
- Micro-segmentation
- Real-time monitoring
- Policy-based and risk-based access control
Key Benefits of Zero Trust Security Architecture
Implementing Zero Trust can bring significant benefits to enterprises and organizations, including:
1. Strengthening Comprehensive Security Against Advanced Threats
Zero Trust helps organizations defend against threats such as ransomware, phishing, compromised accounts, and insider risks.
By enforcing least-privilege access and continuous verification, businesses can significantly reduce the risk of attackers exploiting exposed credentials to access sensitive systems and data.
2. Reducing the Risk of Data Breaches
Since every access request must be verified, attackers cannot easily reach sensitive data even if they manage to compromise an account or device.
This helps limit unauthorized access, reduce lateral movement within the system, and minimize the potential impact of security incidents.
3. Improving Monitoring and Incident Detection
Zero Trust enables organizations to monitor user behavior, devices, applications, and access activities in real time.
With stronger visibility across the digital environment, businesses can detect unusual activities earlier, respond to risks more quickly, and improve their overall incident response capability.

4. Supporting Remote Work, Cloud, and Hybrid Infrastructure
With Zero Trust, users can securely access enterprise resources from anywhere, as long as their identity, device, and access permissions are properly verified.
This is especially valuable for remote and hybrid work models, where employees may access corporate systems from different locations, networks, and personal devices.
5. Enhancing Regulatory Compliance
Zero Trust provides a unified governance framework for enforcing security policies, authenticating users, managing access rights, and maintaining activity logs.
This allows organizations to better meet data protection and information security requirements in highly regulated sectors such as finance, banking, healthcare, telecommunications, and government.
6. Optimizing Long-Term Security Costs
While Zero Trust implementation may require initial investment, it can help optimize security costs in the long run.
By consolidating security controls, reducing the likelihood of data breaches, and limiting damage when incidents occur, Zero Trust helps organizations build a more sustainable and cost-effective cybersecurity strategy.
A Comprehensive Zero Trust-Based Security and Fraud Prevention Solution for BFSI Organizations
With deep experience in the Finance and Banking sector and a proven track record of implementing projects for major banks, SAVYINT introducs e a comprehensive security and fraud prevention solution built on Zero Trust Architecture. Aligned with the core pillars of modern Zero Trust, SAVYINT’ solution enables end-to-end protection across users, devices, applications, data, and digital transactions:
+ Identity verification and user access control
- Strengthen user authentication: Support FIDO2/Passkey and biometric authentication such as fingerprint and facial recognition.
- Require additional authentication based on context and risk level.
+ Establish device trust
- Protect trusted devices through unique Device Fingerprint creation and cryptographic key generation.
- Generate cryptographic keys bound to devices.
+ Real-time application protection with RASP+
+ API security and third-party connectivity
- Strengthen APIM security and control access between banks, customers, and TPPs.
- Comply with international standards such as OAuth 2.0, OpenID Connect, FAPI 1.0 & 2.0, DCR, and PSD2/PSD3.
- Apply JWS digital signatures and data encryption to ensure integrity, authentication, and security during data exchange.
+ Consent management and personal data protection
+ AI/ML integration, transaction risk assessment, and real-time fraud prevention
- Develop a Risk Engine to score risk for each transaction.
- Detect behavioral anomalies with Behavioral Biometrics.
- Protect high-value transactions with Dynamic Linking.
+ Automated compliance reporting
+ Support compliance with Vietnamese regulations, including Circular 50, Circular 64, Circular 77 of the State Bank of Vietnam, Decree 356, the Data Protection Law, and the Cybersecurity Law,…; international standards such as eIDAS, GDPR, and PCI-DSS…; and regional regulations such as Malaysia’s PDPA and RMiT, and the Philippines’ AFASA and BSP 1213–1215…
Connect with SAVYINT experts today to take the lead in enterprise-wide security and fraud prevention!







