Vietnam’s financial and banking sector is entering a phase of significantly tightened requirements for security, data protection, and fraud prevention. From Circular 50, Circular 77, and Circular 64 issued by the State Bank of Vietnam, to the Personal Data Protection Law, Decree 356, and the Cybersecurity Law 2025, financial institutions are no longer required to simply have security systems – they must prove that these systems are reliable, secure, and capable of real-time risk control.
Over the past five years, regulations in Vietnam’s financial and banking sector have clearly shifted – from system-level security requirements to comprehensive control and enhanced protection across the entire digital customer journey. Notably, since 2024, the Vietnamese government has introduced a series of policies to strengthen information security, data protection, and cybersecurity.
Online Service Security
Circular 50/2024/TT-NHNN establishes a comprehensive foundation for securing online banking services, covering customer authentication, transaction data protection, and responsibilities for guiding users about risks.
However, the real tightening comes with Circular 77/2025/TT-NHNN, which amends Circular 50 and takes effect from March 1, 2026. Accordingly, financial institutions must place strong emphasis on endpoint security (Mobile Apps). Mobile banking applications are required to automatically log out or stop functioning if detecting: rooted/jailbroken devices, emulators, debuggers, etc. Server systems must implement version control mechanisms, prevent users from downgrading versions, and ensure software is protected against the top 10 common vulnerabilities (OWASP). Stronger identity verification is required in high-risk scenarios, mandating biometric authentication combined with high-level verification when customers change identity documents or authentication methods.
Circular 64/2024/TT-NHNN sets strict technical standards for open system connectivity architecture, requiring data structures using JSON or XML via REST APIs. APIs must be digitally signed (JWS) and encrypted. It also mandates identity and access management between banks, customers, and third parties (TPPs) based on OAuth 2.0 standards.
Personal Data Protection
The Personal Data Protection Law No. 91/2025/QH15, effective from January 1, 2026, marks a significant milestone in privacy protection in Vietnam. The law requires technical controls embedded directly into system architecture, including mandatory encryption/decryption of sensitive data, implementation of data anonymization processes to prevent re-identification, and compulsory impact assessments for data processing and cross-border data transfers. Systems involving Big Data, AI, Blockchain, and Cloud must integrate appropriate security measures with strict access controls.
Additionally, the law requires the establishment of identity governance mechanisms based on user consent, with features allowing customers to monitor, view, modify, or withdraw their consent.
Decree 356/2025/NĐ-CP, which guides the implementation of the law and replaces Decree 13/2023, establishes a robust technical and legal “barrier,” requiring organizations to implement dual verification mechanisms in personal data processing. Systems must support verifiable consent logging (e.g., OTP, voice recordings, SMS). Access to sensitive data requires strong authentication methods, at minimum multi-factor authentication (MFA), combining passwords with OTP, digital signature devices, or biometrics. These requirements exceed the capabilities of most existing identity and access management systems.
Cybersecurity
The Cybersecurity Law 2025, effective July 1, 2026, establishes a framework for protecting information systems based on five risk levels. It clearly defines the responsibility of online service providers to verify user information during digital account registration and secure user account data. This compels financial institutions to treat digital security as a core capability rather than a supporting technical function.
Zero Trust Architecture
Zero Trust is a modern security architecture based on the principle “Never trust, always verify,” designed for complex and distributed systems. Instead of inherently trusting users or devices within the network, Zero Trust continuously verifies five key pillars: user identity, devices, networks, applications, and data. Every access request must be authenticated, authorized, and continuously monitored. This model enforces strict control over identity, device posture, applications, data, and user behavior in real time.
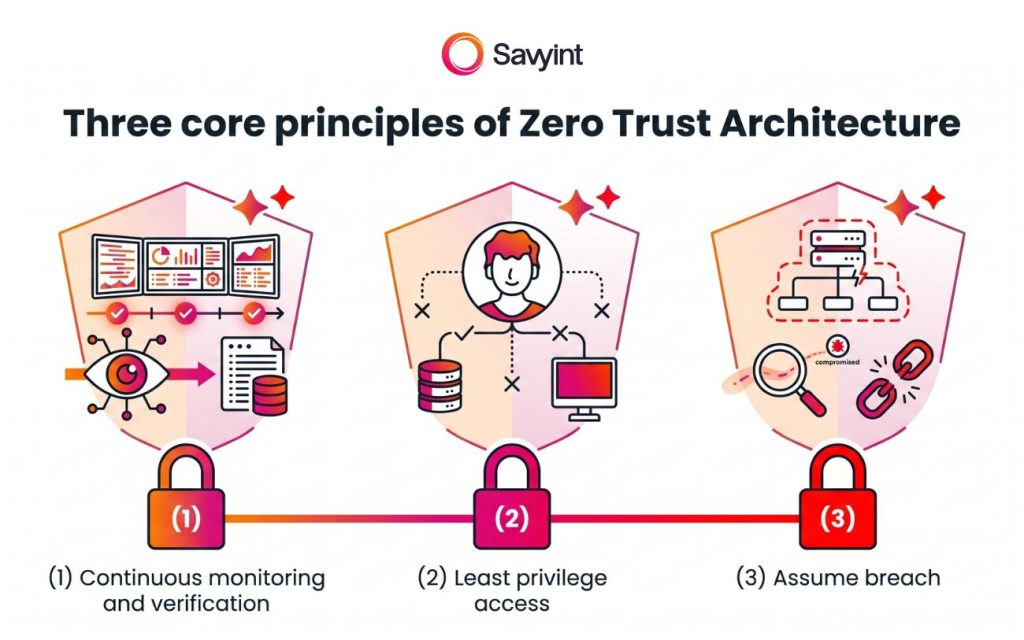
The three core principles of Zero Trust include:
- Continuous monitoring and verification: Network assets are not accessible by default. Every connection request must pass contextual checks (location, device status, abnormal behavior) at all times.
- Least privilege access: Users are granted only the minimum access necessary to perform their tasks, and access is revoked immediately after the session ends.
- Assume breach: Systems are always assumed to be compromised, requiring network segmentation, continuous monitoring, and real-time response.
By applying these principles, Zero Trust helps organizations reduce cyberattack risks, limit lateral movement within systems, and protect digital assets across cloud, mobile, IoT, and remote working environments.
Comprehensive Security and Fraud Prevention Solution for Banks
With extensive experience in the financial and banking sector, Savyint introduces a comprehensive security and fraud prevention solution based on Zero Trust architecture. This solution enables financial institutions to comply with stringent legal requirements both domestically and internationally while addressing key challenges including user authentication, device and application protection, API security, consent management, fraud prevention, transaction risk control, and compliance:
- Strengthening API security management (APIM) in compliance with international standards such as OAuth 2.0, OpenID Connect, FAPI 1.0 & 2.0, DCR, PSD2/PSD3, with JWS digital signing and data encryption for secure access control between banks, customers, and TPPs.
- Customer consent management, enabling banks to record, manage, and retrieve user consent for data collection, processing, and sharing, ensuring transparency and compliance with personal data protection requirements.
- Device Trust protection through device fingerprinting and cryptographic key generation.
- Application protection with RASP+, enabling detection of risks such as root/jailbreak, tampering tools, malware, emulators, and application attacks.
- Enhanced user authentication with support for FIDO2/Passkeys and biometric authentication (fingerprint, facial recognition).
- Fraud prevention system (Risk Engine) that scores transaction risk based on device, location, user behavior, transaction history, and anomalies to trigger step-up authentication, deny, or restrict access.
- High-value transaction protection via dynamic linking, binding transaction details (amount, beneficiary) with authentication codes, biometric verification, and liveness detection to prevent tampering.
- Contextual and behavioral anomaly detection (Behavioral Biometrics) and account change monitoring to trigger responses and prevent account takeover.
- Deep integration with AML & fraud prevention systems to detect money laundering indicators, sudden account activity spikes, multi-layer fund transfers, enabling early warnings and real-time intervention.
- Immediate disabling of high-risk accounts/devices and temporary suspension of outgoing transactions until identity verification is completed.
- Automated compliance reporting, with systems that collect logs, aggregate data, and generate governance, risk, and compliance reports.
Beyond compliance with Vietnamese regulations, Savyint’s security and fraud prevention solutions also strictly adhere to international standards such as eIDAS, GDPR, PCI-DSS, as well as regional regulations in countries like Malaysia (PDPA, RMiT) and the Philippines (AFASA, BSP 1213-1215).
Connect with Savyint experts today to ensure secure operations and full compliance with both domestic and international regulations.







