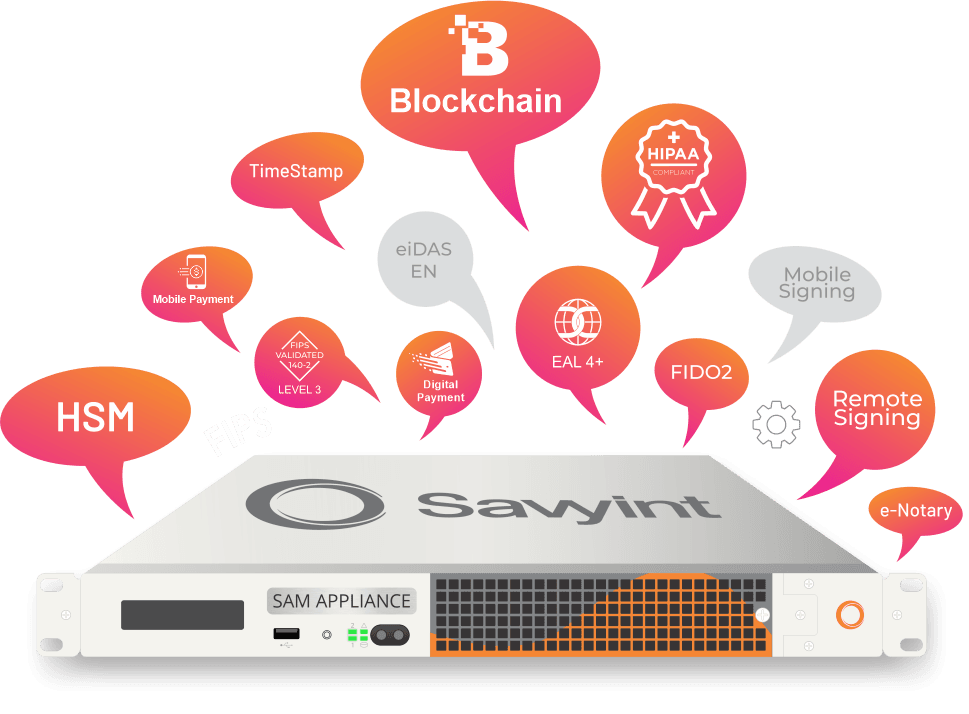
SAM Appliance
An all-in-one solution for data encryption, digital signature authentication and mobile identification
SAM Appliance
An all-in-one solution for data encryption, digital signature authentication and mobile identification
SAM Appliance with Internal HSM - nShield Solo PCIe

Suitable for: Businesses using a digital signature system for the first time or for testing systems, with reasonable initial investment costs.
-
HSM device: nShield Solo PCIe connect directly to the
SAM Appliance server
SAM Appliance with External Network HSM - nShield Network HSM

Suitable for: Medium to large-scale businesses with significant, complex digital signature needs, requiring a systematic and rigorous process automation
-
HSM device: nShield Netwourk HSM is installed separately from
the server
Full compliance with international standards
- Server Appliance with FIPS 140-2 level compliance
- Compliance with ISO 9001:2015, ISO 14001:2015 and ISO 27701:2022
- Data Center compliance standards: GDPR, SOC 2 Type II, HIPAA & PCI DSS
- HSM Hardware: FISP 140-2 Level 3, FIPS 140-3 Level 3, CC EAL4+ AVA_VAN.5 or Common Criteria EAL4+ (EN 419 221-5) certified
- Rest API Service Interface
- Real-time validation with CRL and OCSP
- Compliance with Payment Services Directive (PSD2) on Customer Authentication
- Adherence to General Data Protection Regulation (GDPR)
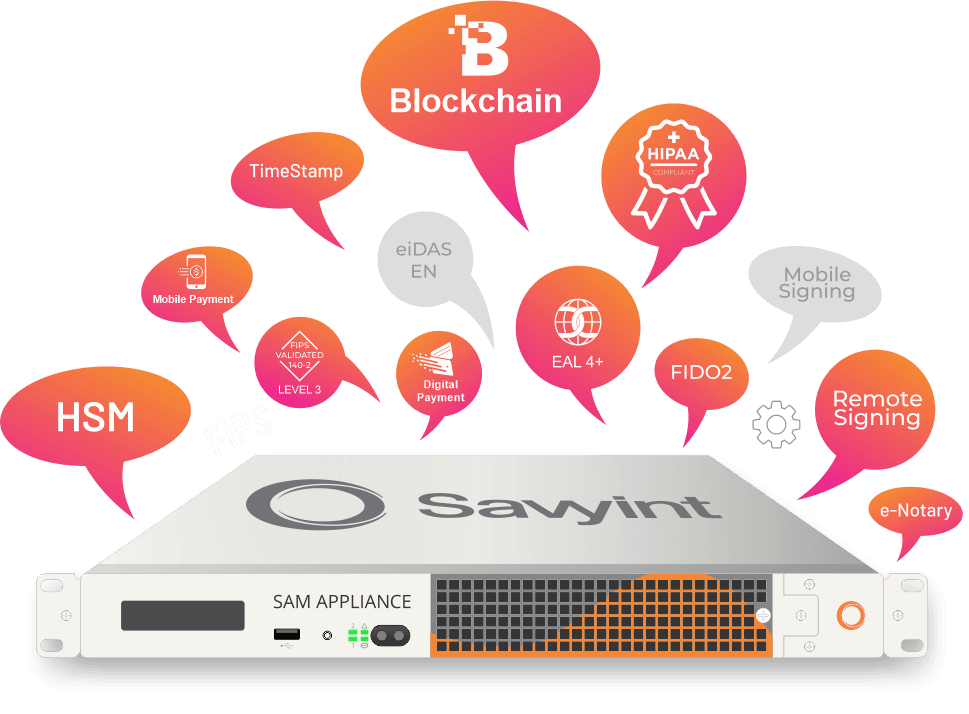
Features

Electronic Identification
Verify user identities in applications, ensuring reliability, accuracy, and security for electronic transactions, while complying with state and European eIDAS regulations.

Secure Digital Signatures
Support advanced signature standards such as ISO 17090 standards like CadES, PadES, XadES, as well as LTV and LTANS standards for electronic storage and authentication.

Blockchain/Cryptocurrency
Manage keys and generate digital signatures within the blockchain system, ensuring authentication, safety, and security for all data and digital assets/cryptocurrencies.
Mobile Payment/Digital Wallet
Integrate with electronic transaction systems and e-wallets to ensure secure online payment transactions with authentication, management, and digital signature generation.

PKI In A Box
Deploy a public key infrastructure (PKI) infrastructure, packaged in a hardware device, to meet the need for building a specialized internal public infrastructure.

Data Encryption -
Transaction Encryption
Encrypt data and transactions, ensuring that all information cannot be stolen or tampered with during initiation, storage, and transmission.

Timestamping
Apply timestamping to data and documents to establish evidence and authenticate the existence of data at a specific point in time.

Electronic Storage
Have the ability to integrate with long-term electronic storage systems, allowing high-quality document storage for 10 years, 20 years, 50 years, or indefinitely.

System Authentication and Security
Compute and log all signing operations, system operations, ensuring traceability and control of activity history.

Dynamic Workflow and System Integration
Initiate, review, and digitally sign documents from mobile devices such as laptops, tablets, and mobile phones
